Digital Communication Evolution
Humanity has a long history of communicating through various means, starting from simple cave paintings to the complex digital networks of today. The introduction of electricity in the 19th century marked a significant shift in communication methods. In 1844, Samuel Morse sent the first telegraph message, posing the question, “What hath God wrought?” This historic moment set the stage for a new era of rapid communication.
From Single-Use Machines to Time-Sharing
The development of digital computers during World War II revolutionized information processing. Initially designed for specific tasks like calculating artillery trajectories, these machines evolved into more versatile tools as their processing power increased. The concept of time-sharing emerged as a cost-effective solution to maximize computer usage. By allowing multiple users to interact with a single machine simultaneously, time-sharing made computing resources more accessible and efficient.
The Birth of Networked Communication
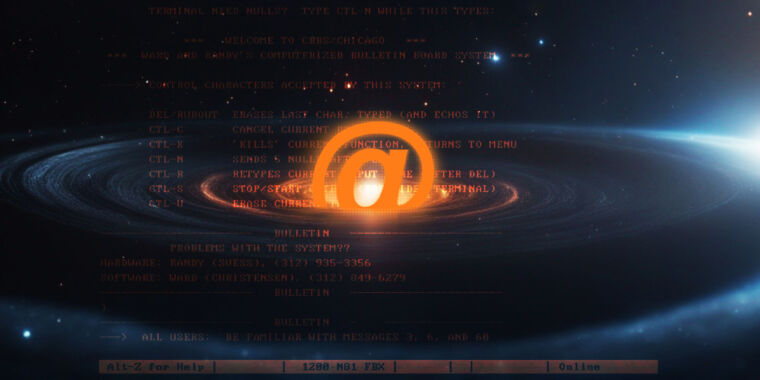
In the late 1960s, the Advanced Research Projects Agency (ARPA) introduced the ARPANET, a revolutionary network that connected different computers through the use of Interface Message Processors (IMPs). This breakthrough allowed users to send messages across vast distances, paving the way for global communication. Ray Tomlinson’s creation of the first inter-computer messaging program, SNDMSG, in 1971, introduced the concept of email with the iconic “@” symbol.
The Impact of PLATO Network
Simultaneously, the PLATO educational system was making waves in the digital world. Launched in 1960, PLATO featured cutting-edge technology, including the world’s first flat-screen plasma display in 1972 with PLATO IV. This touch-enabled graphical interface revolutionized educational communication, enabling users worldwide to interact seamlessly.
In 1971, PLATO faced its first cybersecurity incident when a student devised a phishing scam to steal passwords. This event prompted the implementation of a security feature, SHIFT-STOP, to protect users from unauthorized access. This proactive security measure foreshadowed later cybersecurity practices, such as CTRL-ALT-DEL in Windows NT.
Image/Photo credit: source url